THE ZERO: Anne Wojcicki / 23andMe
The story: In October 2023, hackers breached 23andMe, initially accessing about 14,000 accounts through credential stuffing. But because of the company's DNA Relatives sharing feature, that small breach cascaded into the exposure of 6.9 million users—nearly half the company's customers—including highly sensitive genetic and ancestry data.
When victims filed lawsuits, 23andMe's response was extraordinary: blame the victims.
"23andMe believes that unauthorized actors managed to access certain user accounts in instances where users recycled their own login credentials... users negligently recycled and failed to update their passwords following these past security incidents, which are unrelated to 23andMe."
"Therefore, the incident was not a result of 23andMe's alleged failure to maintain reasonable security measures," the letter reads.
The company went further, arguing that the stolen data "cannot be used for any harm."
Attorneys representing victims called the response "nonsensical":
"This finger pointing is nonsensical. 23andMe knew or should have known that many consumers use recycled passwords and thus that 23andMe should have implemented some of the many safeguards available to protect against credential stuffing — especially considering that 23andMe stores personal identifying information, health information, and genetic information on its platform."
Critically, "The breach impacted millions of consumers whose data was exposed through the DNA Relatives feature on 23andMe's platform, not because they used recycled passwords. Of those millions, only a few thousand accounts were compromised due to credential stuffing."
Prior to the data breach in October, 23andMe did not mandate the use of 2FA.
A PR expert called the response a complete miss:
"From a crisis comms standpoint, 23andMe's response to its breach misses the mark completely. The decision to blame the victims has fuelled negative press, dodged responsibility, and failed to express any compassion towards those impacted."
Within days of the new year, 23andMe took to deflecting the blame for the massive data theft onto the victims. Lawyers representing the group of hundreds of 23andMe users who sued the company following the hack said the finger-pointing was "nonsensical."
The company eventually laid off 40% of staff and declared bankruptcy on March 23, 2025.
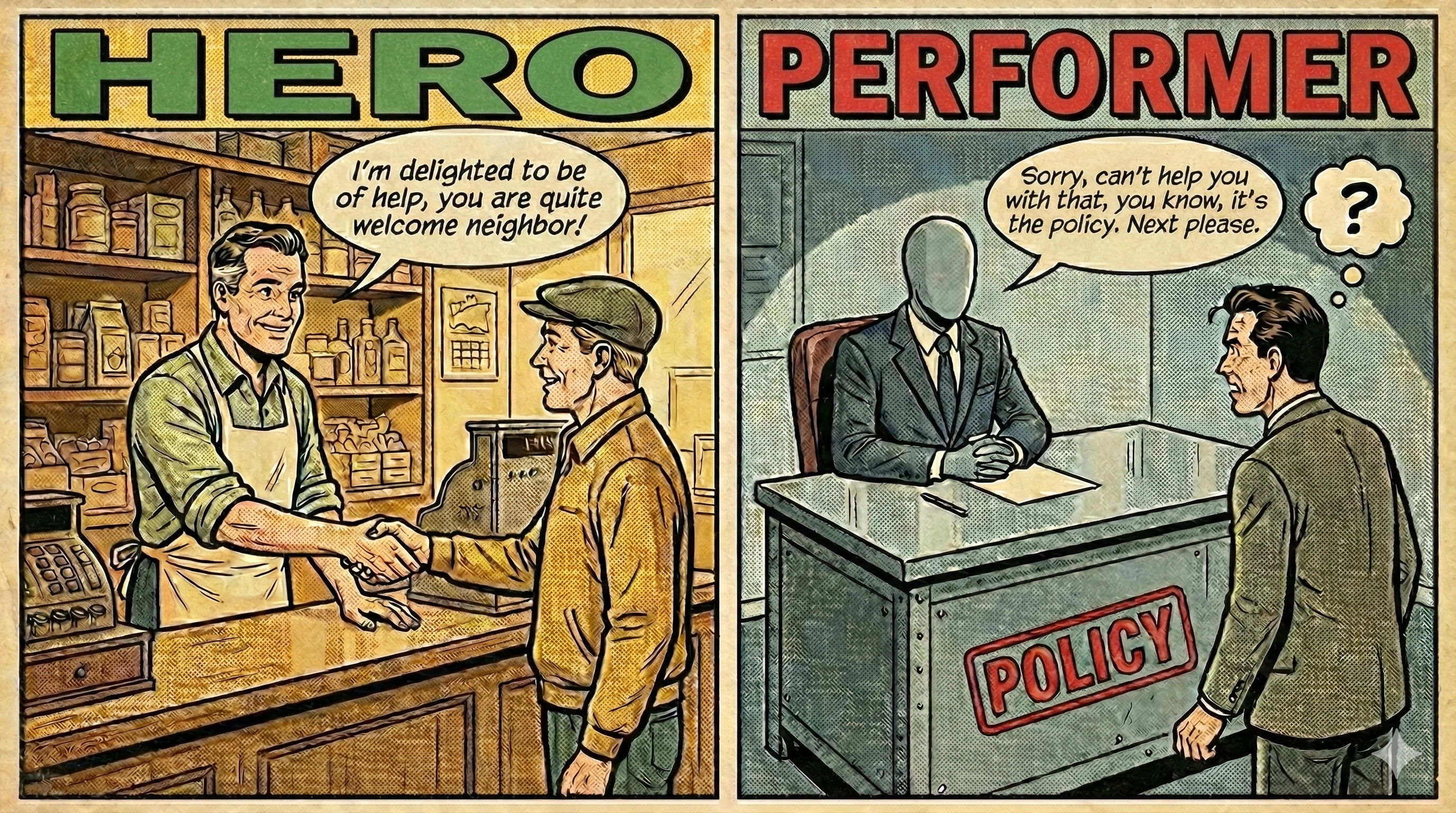
Why it's performer: 23andMe's mind was filled with one question: "How do we avoid liability?"
The answer: blame your customers. Call them "negligent." Claim their exposed genetic data "cannot be used for any harm."
Never mind that the company didn't require two-factor authentication. Never mind that 6.9 million people were exposed because of a design flaw in their platform—not because those users reused passwords. Never mind that the company holds some of the most sensitive personal data imaginable.
When your security fails, blaming customers doesn't protect them. It protects your legal position.
THE HERO: Dara Khosrowshahi, Uber
The story: When Dara Khosrowshahi became Uber CEO in August 2017, he inherited a cover-up. The previous leadership had concealed a 2016 data breach that compromised 57 million riders and drivers—and paid the hackers $100,000 in bitcoin to stay quiet, disguising it as a "bug bounty."
Khosrowshahi could have continued the cover-up. Instead, he investigated.
"After the facts in this email did not match the accounting from the special matters committee that led to my initial inquiry — there were some differences — I had to understand which was the correct version of the truth," Khosrowshahi said. He said he authorized Uber to hire an outside firm "to understand what happened."
He said the firm's findings led him to believe he needed to disclose the incident, which Uber did via a public blog post on Nov. 21, 2017.
Then Khosrowshahi fired the security chief responsible:
"I decided to fire Joe because he was my chief security officer and I couldn't trust his judgment anymore."
In a statement about the breach, Khosrowshahi acknowledged that the hackers "downloaded files" containing user information and apologized to those affected.
Prosecutors claimed that if not for the "fortuitous arrival" of the new Uber CEO, Dara Khosrowshahi, in August 2017, Sullivan would most likely have gotten away with the cover-up.
"There is every reason to believe the tens of millions of victims of the 2016 Data Breach never would have learned about it."
The disclosure cost Uber $148 million in fines. But Khosrowshahi chose transparency anyway.
Why it's heroic: Khosrowshahi's mind was filled with one question: "What do affected customers deserve to know?"
He didn't inherit the breach—he inherited the cover-up. He could have let it stay buried. Instead, he investigated, disclosed, apologized, and fired the person responsible.
The $148 million fine was the price of doing the right thing. But that fine gave 57 million people the information they needed to protect themselves.
THE FRAMEWORK
| Aspect | Performer (23andMe) | Hero (Khosrowshahi) |
|---|---|---|
| The breach | 6.9M users exposed via design flaw | 57M users exposed via hack |
| Response | Blamed users for "negligent" passwords | Investigated, disclosed, apologized |
| Security posture | No mandatory 2FA before breach | Hired new security team after disclosure |
| Who bore cost | Victims blamed, left unprotected | Company paid $148M in fines |
| Legal strategy | "Users are at fault, data can't cause harm" | Full disclosure despite legal exposure |
| Outcome | Bankruptcy (2025) | Rebuilt trust, company survived |
| Mind filled with | Legal liability protection | Customer protection |
THE LESSON
Both companies experienced massive data breaches. The difference is entirely in the response.
23andMe argued that because 14,000 accounts were breached through credential stuffing, all 6.9 million victims were at fault. This is like arguing that because a thief picked one lock, everyone in the building deserved to be robbed.
The company didn't require two-factor authentication. They designed a system where one breached account could cascade to millions of others. Then they blamed customers for not having better passwords elsewhere.
Khosrowshahi walked into a cover-up and chose disclosure—knowing it would cost the company hundreds of millions of dollars. He fired the person responsible. He apologized to affected users.
"Publicly downplaying the risk and deflecting blame is undoubtedly poor PR."
But it's worse than poor PR. It's revealing what fills your mind.
When your security fails, you have a choice: protect your customers or protect your legal position. You can't do both at the same time.
The hero asks: "What do the people I've harmed need from me?"
The performer asks: "How do I avoid paying for this?"
23andMe chose to argue that genetic data "cannot be used for any harm" while millions of people wondered what would happen to their most intimate biological information. They chose legal defense over customer defense.
Khosrowshahi chose to pay $148 million so that 57 million people could take steps to protect themselves. He chose customer defense over legal defense.
One company went bankrupt. One company survived and rebuilt trust.
The hero doesn't blame victims for being victimized. The hero takes responsibility for failing to protect them.